China’s largest reported data breach exposed the records of nearly one billion individuals and demonstrated how a single cybersecurity failure can create catastrophic operational, financial, and compliance consequences.
The breach revealed critical weaknesses in:
- cloud security infrastructure
- payment data protection
- access control management
- database monitoring
- cybersecurity governance
- secure payment processing systems
Businesses processing electronic payments remain primary cybercrime targets because payment environments contain high-value financial information that can be rapidly monetized through fraud, ransomware, account takeover attacks, and merchant account compromise.
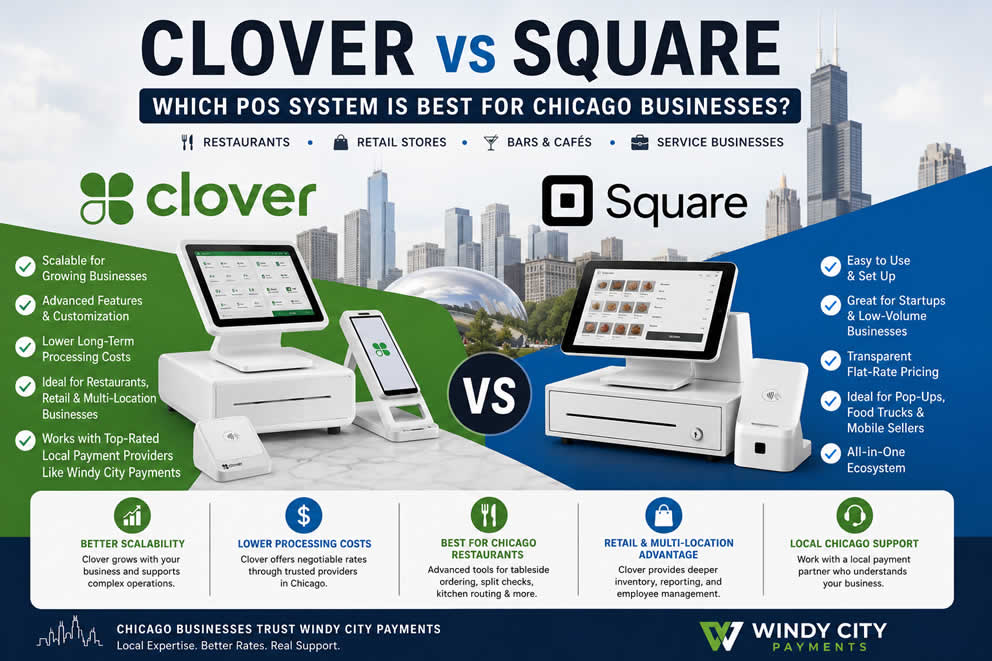
Secure payment processing is now a core operational requirement for:
- restaurants
- retail businesses
- healthcare providers
- eCommerce companies
- contractors
- hospitality businesses
- professional service firms
Organizations using outdated payment systems face elevated exposure to payment fraud, PCI compliance violations, ransomware attacks, and operational disruption.

What Is Secure Payment Processing?
Secure payment processing refers to the technologies, compliance standards, encryption systems, and fraud prevention controls used to protect payment transactions and customer financial data.
Secure payment processing systems help businesses:
- protect customer cardholder data
- reduce payment fraud
- prevent unauthorized transactions
- maintain PCI compliance
- secure merchant accounts
- reduce chargebacks
- prevent ransomware-related payment disruption
Modern secure payment processing environments typically include:
- encrypted payment gateways
- EMV-enabled terminals
- tokenization systems
- PCI-compliant payment infrastructure
- fraud monitoring tools
- secure cloud payment systems
Key Lessons From China’s Largest Data Breach
| Cybersecurity Lesson | Business Impact |
|---|---|
| Misconfigured cloud systems create massive exposure | Unauthorized access to customer data |
| Weak payment security increases fraud risk | Financial and reputational losses |
| Delayed breach detection increases damage | Larger operational disruption |
| Poor compliance controls increase liability | Regulatory penalties and lawsuits |
| Insecure payment systems attract cybercriminals | Merchant account compromise |
Lesson 1: Cloud Security Failures Create Payment Security Risk
Many businesses incorrectly assume cloud systems are automatically secure.
Cloud infrastructure providers supply hosting environments, but businesses remain responsible for:
- access permissions
- database visibility
- encryption controls
- API security
- user authentication
- monitoring systems
Many enterprise breaches originate from simple configuration failures rather than advanced hacking techniques.
Common Cloud Security Failures
| Security Failure | Payment Security Risk |
|---|---|
| Public-facing databases | Customer payment exposure |
| Weak passwords | Credential theft |
| Unsecured APIs | Payment data extraction |
| Disabled monitoring | Delayed fraud detection |
| Excessive employee permissions | Internal misuse |
| Outdated software | Exploitable vulnerabilities |
Business Consequences of Weak Cloud Security
- payment fraud
- PCI compliance violations
- ransomware attacks
- operational downtime
- customer lawsuits
- regulatory investigations
- reputation damage
Recommended Cloud Security Controls
- multi-factor authentication (MFA)
- zero-trust access architecture
- end-to-end encryption
- role-based permissions
- continuous vulnerability scanning
- real-time threat monitoring
Lesson 2: Secure Payment Processing Reduces Fraud Exposure
Payment environments remain among the highest-value cybercrime targets.
Restaurants, retail stores, healthcare providers, and small businesses process sensitive customer payment information across:
- POS systems
- mobile payment systems
- payment gateways
- online ordering platforms
- merchant accounts
- invoicing software
Businesses using secure payment processing systems reduce exposure to:
- card skimming attacks
- POS malware
- credential theft
- ransomware
- chargeback fraud
- unauthorized transactions
Most Frequently Targeted Payment Data
| Payment Data | Criminal Objective |
|---|---|
| Credit card numbers | Fraudulent purchases |
| ACH banking information | Unauthorized transfers |
| Merchant credentials | Account takeover |
| Payroll records | Identity theft |
| Customer billing data | Financial fraud |
PCI Compliance and Secure Payment Processing
PCI compliance helps businesses protect cardholder data and reduce payment security risk.
Businesses processing credit card payments must maintain secure payment environments that meet PCI DSS requirements.
Core PCI Compliance Requirements
| PCI Requirement | Security Purpose |
|---|---|
| Encrypt payment data | Prevent unauthorized access |
| Restrict system access | Reduce internal exposure |
| Monitor payment systems | Detect suspicious activity |
| Maintain secure networks | Prevent intrusions |
| Test security systems | Identify vulnerabilities |
| Maintain access controls | Protect sensitive data |
Benefits of PCI Compliance
- reduced fraud exposure
- improved customer trust
- stronger payment security
- lower breach risk
- improved merchant account stability
- reduced legal liability
MV Payment Processing and NFC Payment Security
Modern secure payment processing systems should support:
- EMV payment processing
- NFC payment processing
- tap-to-pay transactions
- encrypted mobile payments
- tokenized payment environments
EMV Payment Processing Benefits
| EMV Security Feature | Business Benefit |
|---|---|
| Chip authentication | Reduced counterfeit fraud |
| Dynamic transaction codes | Improved payment security |
| Encrypted transaction data | Reduced card theft risk |
| Secure terminal communication | Lower fraud exposure |
NFC Payment Processing Benefits
NFC payment processing allows secure contactless payments using encrypted wireless communication between payment devices and payment terminals.
Businesses using NFC payment systems improve:
- transaction speed
- payment security
- customer convenience
- fraud protection
Lesson 3: Delayed Threat Detection Increases Breach Costs
Most businesses fail to detect cyber intrusions immediately.
Attackers frequently remain inside compromised systems for extended periods while escalating permissions, extracting payment information, and expanding access across networks.
Longer detection timelines significantly increase:
- financial losses
- fraud exposure
- operational downtime
- legal liability
- recovery expenses
Average Impact of Delayed Detection
| Detection Timeline | Business Impact |
|---|---|
| Within hours | Minimal disruption |
| Several days | Increased fraud exposure |
| Several weeks | Significant financial losses |
| Several months | Severe operational damage |
Warning Signs of a Cyberattack
- suspicious payment failures
- unusual network traffic
- unauthorized administrator access
- missing customer records
- ransomware alerts
unknown software installations
Threat Detection Technologies
- SIEM platforms
- endpoint detection and response (EDR)
- intrusion detection systems (IDS)
- managed threat monitoring
- AI-based anomaly detection
- real-time alert systems
Lesson 4: Small Businesses Require Secure Merchant Services
Small businesses remain primary cyberattack targets because attackers often expect:
- weaker security infrastructure
- outdated POS systems
- poor monitoring controls
- delayed software updates
- insufficient employee training
Secure merchant services help businesses:
- protect payment data
- secure customer transactions
- reduce fraud exposure
- improve PCI compliance
- maintain operational continuity
Industries Facing Elevated Payment Security Risk
| Industry | Primary Payment Security Risk |
|---|---|
| Restaurants | POS malware and payment theft |
| Retail | Cardholder data exposure |
| Healthcare | Financial and patient data theft |
| eCommerce | Credential stuffing attacks |
| Hospitality | Payment fraud |
| Professional Services | Sensitive billing data exposure |
Secure Payment Processing Checklist for Businesses
Payment Infrastructure Security
- use PCI-compliant payment systems
- encrypt payment transactions
- eliminate unnecessary stored card data
- upgrade outdated POS hardware
- monitor payment anomalies continuously
Cloud Security Controls
- secure cloud payment databases
- enable MFA across all systems
- restrict administrative access
- patch vulnerabilities immediately
- monitor APIs continuously
Employee Security Controls
- conduct phishing awareness training
- enforce password management policies
- restrict privileged access
- secure remote work environments
Incident Response Readiness
- maintain encrypted backups
- test disaster recovery systems
- develop breach response procedures
- document vendor notification protocols
Most Common Payment Security Threats
| Cybersecurity Threat | Primary Objective |
|---|---|
| Ransomware | Financial extortion |
| POS malware | Payment card theft |
| Phishing attacks | Credential theft |
| Business email compromise | Financial fraud |
| Cloud misconfiguration | Database exposure |
| Credential stuffing | Account takeover |
| Insider threats | Unauthorized access |
| API exploitation | Data extraction |
Frequently Asked Questions
What is secure payment processing?
Secure payment processing refers to the technologies and security controls used to protect payment transactions and customer financial data from fraud and cyberattacks.
Why is secure payment processing important?
Secure payment processing reduces fraud exposure, protects customer cardholder data, supports PCI compliance, and improves operational security.
What is PCI compliance?
PCI compliance is a security standard designed to protect payment card information and reduce payment fraud risk.
How can businesses improve payment security?
Businesses improve payment security through encryption, PCI-compliant payment systems, EMV terminals, MFA, tokenization, and continuous monitoring.
What industries require secure payment processing the most?
Restaurants, retail stores, healthcare providers, hospitality businesses, eCommerce companies, and professional service firms face the highest payment security risk.
What is EMV payment processing?
EMV payment processing uses chip-enabled payment cards and encrypted authentication technology to reduce counterfeit card fraud.
What is NFC payment processing?
NFC payment processing enables secure contactless payments through encrypted wireless communication between payment devices and terminals.
Why are restaurants frequently targeted by cybercriminals?
Restaurants process high transaction volumes and often operate outdated POS systems, making them attractive targets for payment fraud and ransomware attacks.
What are the warning signs of a payment system breach?
Suspicious payment failures, unusual network activity, unauthorized administrator access, ransomware alerts, and missing customer records are common indicators.
How does tokenization improve payment security?
Tokenization replaces sensitive cardholder information with secure digital tokens that reduce the risk of payment data theft.
Why do small businesses face elevated cybersecurity risk?
Small businesses often operate with weaker security controls, outdated software, limited monitoring systems, and slower incident response capabilities.
How does secure payment processing reduce chargebacks?
Secure payment processing systems use encryption, fraud monitoring, authentication controls, and secure transaction verification to reduce fraudulent disputes and unauthorized transactions.
What role does MFA play in payment security?
Multi-factor authentication helps prevent unauthorized access to payment systems, cloud databases, merchant accounts, and administrative environments.
Why are cloud payment systems vulnerable?
Cloud payment systems become vulnerable when businesses fail to secure permissions, encryption controls, APIs, and monitoring systems properly.
How often should businesses perform cybersecurity assessments?
Businesses should conduct cybersecurity assessments quarterly and continuously monitor critical payment systems for vulnerabilities and suspicious activity.



We didn’t invent the term “fools with tools.” Still, it’s a perfect definition for the practice of buying a stack of sophisticated cybersecurity technology that’s impossible to manage without an MSP or the budget of a Fortune 500 IT department.